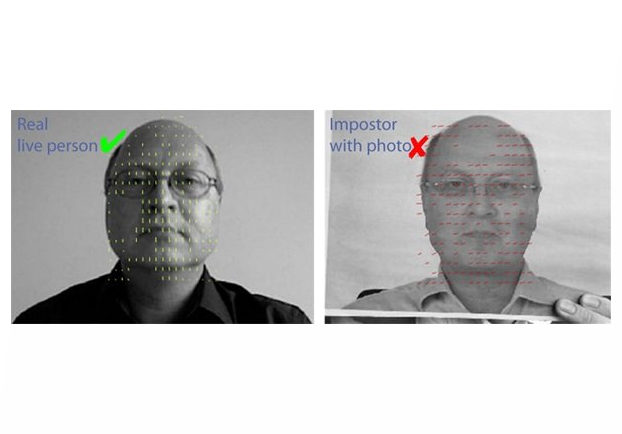
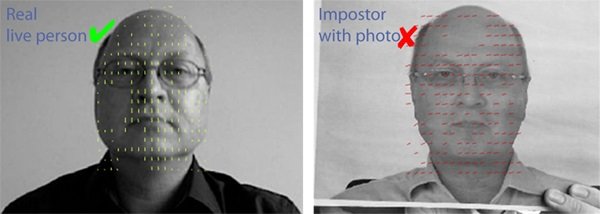
One of the top advantages of biometric authentication is that, unlike a password or token, the credentials can’t be stolen. However, they can be copied. In the case of face recognition, it is easy for a determined attacker to get a photo or video of their victim, either in person or through social media, and use it to attempt biometric fraud in the form of a replay attack. In order to ensure that biometric traits are presented by a live person and not a photo or recording, even in unsupervised authentication applications such as online login or mobile payments, several techniques for face liveness detection have been developed. However, some are more effective than others.
Liveness detection techniques in face recognition against biometric fraud
Sophisticated techniques use 3D cameras to look for depth information from a 3D face, or infrared cameras to detect thermal information. However, both require special expensive equipment and so are not compatible with most webcams and mobile phone cameras available today.
Perhaps the most common method seen today is eye blinking detection. But, many blink detection systems can be fooled easily: An attacker can simply take a photo, cut out holes for the eyes, hold it in front of their face and blink. If done carefully this can fool many blink detection systems. A video of the person blinking would also work.
Another technique looks for pupil dilation, for instance by suddendly changing the brightness of a screen. This can successfully detect fakes but is also vulnerable to a photo with eye holes, or to a well-timed video.
One approach often discussed is known as texture detection. Essentially, image-processing algorithms analyze the texture to differentiate between the texture of skin and that of the paper a photo is printed on. While the lab results are impressive, this technique is impractical in real-world applications because it would require training in the texture of every possible paper, fabric, or other surface on which a photo could be printed.
Another method belonging to the field of optical flow algorithms analyzes motion between two or more pictures, because a 3D face moves differently from a 2D photo. The capturing of the second photo can be triggered with motion detection, so that an attacker cannot simply present two slightly different photos; the second image would be captured before the attacker’s 2nd photo was in place. This has proven to be an excellent way to detect fraud using a photo, and is one of the methods BioID uses in its “fake defender”.
This technique can, however, sometimes be fooled by a video of the live user. To avoid a video attack, BioID employs a challenge-response technique. Therefore, the user is directed to turn slightly in a random direction. The photo is analyzed to make sure they turned in the specified direction. With four basic directions (up, down, left, right), a video attacker with a video of a turning head would have a 25% (1 in 4) chance of success. This process can be stacked, with the user asked to turn the head multiple times. Three rounds, for instance, decrease the odds to 1.56% (1 in 64); five rounds increase it to 0.098% (1 in 1024), and so on.
One final approach to combat replay attacks is through the use of multimodal biometrics, where more than one biometric trait is captured. It is much harder for an attacker to successfully fake multiple biometrics, especially when they must be presented at the same time. For instance, BioID offers both face and voice recognition.
With these techniques, BioID can distinguish live faces from photos and videos with a high degree of accuracy, thus guarding against biometric fraud.
Contact
Ann-Kathrin Schmitt
+49 911 9999 898 0
press@bioid.com