
User authentication is the process of verifying a user’s identity in order to grant access to data and services. Traditional authentication relies on passwords, but it is all too clear that this is no longer an acceptable solution. On the one hand, advances in technology have made
it much easier to crack even a difficult password. On the other hand, the sheer number of accounts that an individual must manage has grown to the point where most people cannot remember a different long and complex password for each account.
Studies show,that over two-thirds of Internet users have forgotten a long or complex password at least once in the last two years (Ponemon Institute LLC, 2013). Additionally, 37% have had to ask for help with an online username or password at least once per month (Janrain, 2012).
A better solution is needed that provides greater security while making it easier on legitimate users to access their accounts.
Multifactor authentication
User authentication requires verifying identity through various credentials. Three types of authentication factors can be used:
- Knowledge factor: something you know (e.g. password)
- Possession factor: something you have (e.g. smart card)
- Inherence factor: something you are (e.g. biometrics)
For stronger authentication, multiple factors can be combined. For instance, to get cash at an ATM, you must have a card and enter a PIN. Similarly, many online services require you to enter a code sent to a hardware token after you enter your username and password. Both of these are examples of the first two factors. However, such multifactor authentication is often complicated and inconvenient, and neither of the first two factors verifies the authorized user’s physical presence: a requirement increasingly demanded by both services and their users. Secure multifactor authentication should always require user presence, thus the inherence factor. User presence has been perceived to provide the highest level of assurance, as indicated for instance by UK government identification guidelines. An inherence factor with liveness detection would provide the required verification of user presence.
An ideal solution should not require memorization of any passwords or codes, nor should it require carrying any special hardware device. Such an ideal solution is already possible, since most people today carry with them a mobile phone. Combined with biometrics, a mobile authenticator offers a powerful solution for authentication that is both strong and convenient, and ensures that the user is really present.
Mobile biometrics
What is mobile biometrics? More specifically, what would such a mobile authenticator app look like? For the biometric component it makes most sense to concentrate on biometric traits that can be easily and securely captured using the sensors that are available on every smartphone: the camera and microphone. The most likely biometric features then are face, iris / eye area and voice, all of which have the additional benefit of having almost no learning curve – nearly anyone with a smartphone can take a selfie or speak a pass phrase.
The mobile phone itself acts as an additional factor, since the user must have their device registered or “paired” with the authentication server in order to authenticate. Unlike non-biometric mobile authenticators, however, possession of the phone is not enough, it must be “bound” to the user – in other words, only the authorized user can successfully authenticate, using their unique biometric features on the registered device. Furthermore, with a mobile device it is also possible to step up the security level by taking time and geolocation of access into account (similar to fraud detection used by payment services), so for instance a system could be configured to require stricter liveness detection, multiple biometrics or an additional factor (e.g. a password or one-time code) if the device is located in a high-fraud country or an unfamiliar location, or at a time outside of the normal usage period. Likewise level of assurance could be boosted when the device is used on a trusted Wi-Fi network.
Unified authentication
One of the most exciting possibilities of a mobile authenticator is to use it as a multi-purpose identifier: a unified authenticator across different services or channels. A single app on a single device with a single user experience can be used, for instance, to log into applications or cloud services on home and office PCs, a tablet, and for physical access control to unlock a door, as well as to authorize payments online and in person. This authentication process offers the additional benefit of out-of-band authentication, where identity is verified through a separate channel, thus protecting against man-in-the-middle attacks. Last but not least, using mobile authentication for multiple services also greatly enhances user experience and reduces support costs.
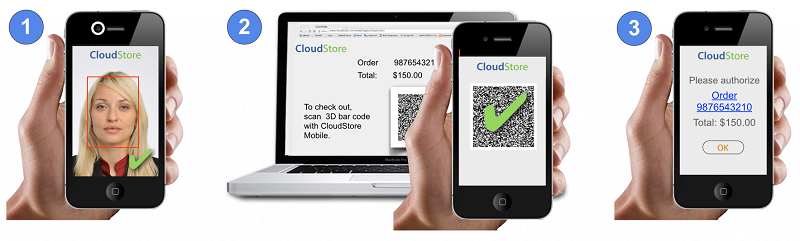
In this case a secure connection between the authenticator device and the PC, door, POS terminal or other device to be accessed can be established in several ways, including via QR code, proximity (Bluetooth, NFC or geofencing), and push notification.
To try out mobile biometric authentication, please download our free app today and explore the possibilities!
Contact
BioID
Ann-Kathrin Schmitt
+49 911 9999 898 0
press@bioid.com